Featured Resource
e-book
Regpack Blog: Smart Invoicing Systems, Payment Automation & Client Management Insights
regpack client spotlights



What is Regpack?
Regpack is an online registration software that creates intelligent application processes with integrated payment processing.
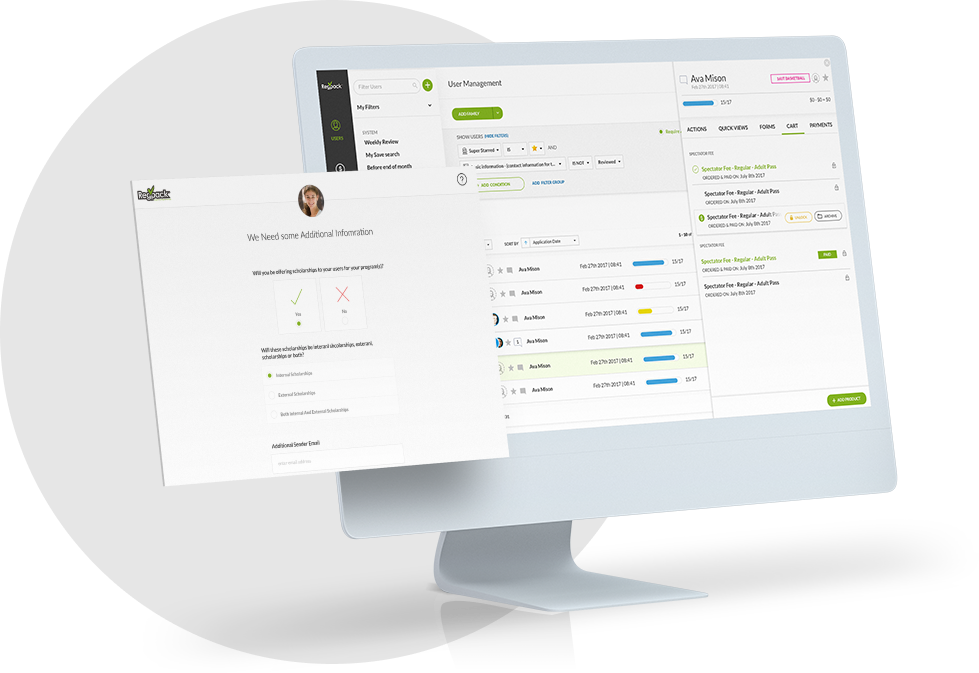
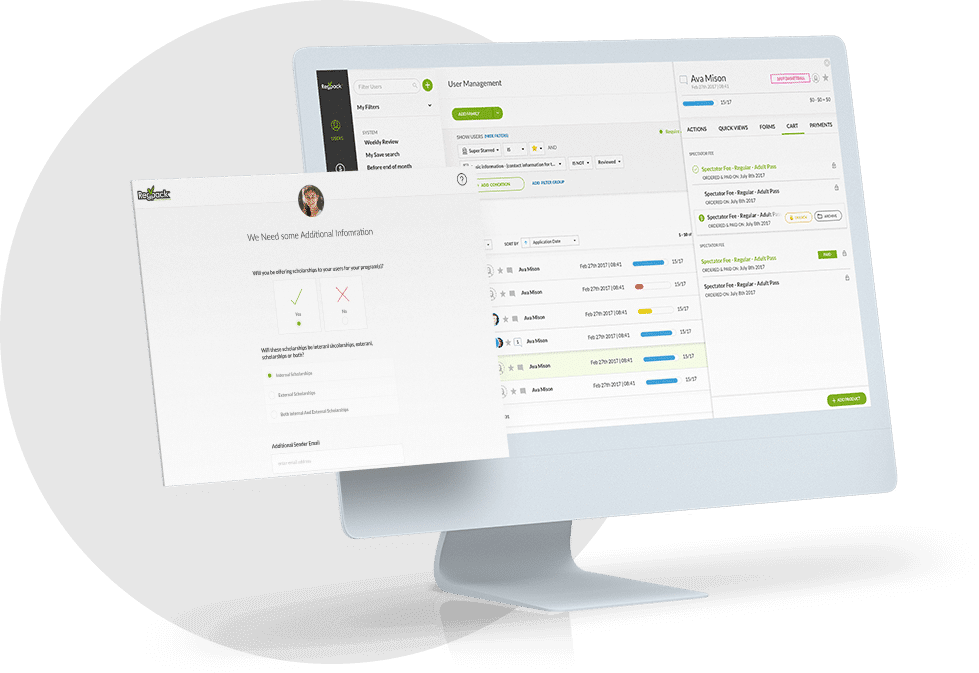
Your Process, Automated
Find and create applicant groups according to YOUR needs. Automate your online registration.
Your Website, Our Technology
Don't send applicants away! Embed your process seamlessly onto your website.
Integrated Payment Processing
Applicants can pay easily within the registration process. Manage payments, send invoices, and more!
Save 60+ Admin Hours Every Month!
Online registration automation tools that work for you! Save time and work smarter.